This post is also available in: Russian
The growing popularity of online video content is a powerful catalyst for Web multimedia portal development. Every day, more and more videos are published and viewed on the Web. As video content production costs are usually much higher than the cost of Web publishing, there is a reasonable desire to protect the valuable assets. Often, if you are going to distribute premium video content on your site, protection requirements are often put forward by the copyright holders. In this article, we will discuss the available content protection tools, giving more detail to Adobe Flash Access 2.0. Also, we’ll familiarize you with the basics of DRM in your projects and share our hands-on experience in implementing DRM based on Adobe Flash Access 2.0.
Web DRM Systems
First of all, we all have to admit that there’s nothing absolute whatsoever. So, there’s no such thing as absolute protection either. There goes a constant struggle between very talented developers on both sides. Protection tools greatly complicate the activities of malicious users and, as a rule, they tend to abandon the idea of illegal copying. However if video content is unprotected, RealPlayer Downloader browser plugin is quite sufficient for video download.
Most DRM systems (including Web based systems, such as Adobe Flash Access 2.0 and Windows Media Rights Management Server) are designed with the same approach in mind. The DRM solution consists of two parts: the content packager and the license server. The packager performs pre-encryption of files, and license server delivers keys to decrypt the content. Content distribution tools are, as a rule, outside the DRM scope, and are implemented by third-party solutions.
There are many DRM vendors today in the market. Also, the market has grown more active recently as Google acquired Widevine. Actually, just two products can be involved with Web projects: Adobe Flash Access 2.0 and Windows Media Rights Management Server (WM RMS).
WM RMS distinctions are:
- Free of charge
- Approved by most major copyright holders
- Obsolete to a large extent
- Windows only
- Inefficient codecs used
- DTO model only supported
- Protection of WMV format only
WM RMS is so popular because it is free. But of all the major successful Internet projects you can scarcely name one based on WM RMS.
Adobe Flash Access 2.0 was released last year and is quickly gaining popularity among Web publishers. Here are the features of Flash Access 2.0:
- Easy portal integration. It requires minimum modifications to Flash video player
- 80% of video on the Internet is Flash based
- Supported by DTO, VoD, and Live Video business models
- This is a cross platform solution, supporting Windows, MacOS, and Linux
- The most efficient modern codecs used
- Approved by most major copyright holders
- Protection of FLV and F4V formats
- Quite pricy
Given the popularity of Flash video on the Internet, we can say that Adobe Flash Access 2.0, despite its high cost, is an ideal solution to implement your video content monetization strategy.
Now some words about open standards and open source. Open Source DRM is in no way possible for the simple reason that no copyright holder will be happy with this idea. First, it is an ideological misconception. How is it possible to protect premium content using public tools? It would be like keeping a deposit box key in front of the box. Second, DRM provider should monitor not only the process of content protection and access restriction levels, but also content display. WM RMS is used to control Windows Media Player, so it only works offline. Adobe controls Flash and AIR, so it works both in offline and online modes. In view of the above, in the next couple of years, protected delivery of online video is most advisable with the Adobe products.
Flash Access allows you to deliver online video over HTTP, as it is transmitted in an encrypted format. From the publisher’s perspective, this offers two major benefits: you can involve traditional CDN providers to optimize content delivery and offer enhanced video quality (the user can pause viewing and load all videos in high quality).
Making a slight digression at this point, we had a unique experience of using multiple DRM systems in one project. This is also possible, offering significant savings to launch the project. For the DTO model (content is downloaded to a user computer) we used WM RMS, and for online viewing Flash Media Server with RTMP was used (such type of protection is also approved by major copyright holders). Such a solution can be very cost-efficient at the first phase of your multimedia project development.
Flash Access
Adobe Flash Access 2.0 is a large-scale and very flexible constructor to create DRM systems run by the Tomcat Java Application Server.
Integrating Flash Access
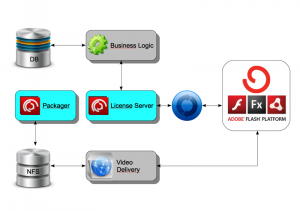
A typical Flash Access 2.0 integration architecture.
To pre-process video content, it is necessary to define protection policies and initiate the encryption process. It is very convenient to integrate the policy management, security and encryption process within a content management system (CMS). You can use a separate rights management system though. This is justified when dedicated employees are involved with licensing, who do not need access to the rest of the content management system. In our CMS, we have implemented different roles, and the license manager can access only the encryption policies and processes. Ultimately, the CMS stores data on content units, the rules of their publication on Web sites, and the rights to use them. Policy management and encryption processes can be easily implemented using the Flash Access Web services. This way, they will easily integrate into any CMS solution.
Protected content can be delivered in any way: independently or using a CDN provider or even through torrents. With flexible delivery over HTTP, you can involve CDN service providers without Flash Media Servers or use your own HTTP servers, which will reduce the infrastructure costs.
The license servers are responsible for restricting access to the content (licensed playback). Flash Access includes several sample implementations of license servers: Standard License Server and the Server for Protected Streaming. A more detailed description of these services is given below. You can implement the business logic to restrict access to content, using a standard authentication mechanism: make a call to an external system (a database or Web service) to verify the content purchase activity (by login, password, content ID, and ID of a client PC). This approach offers the maximum flexibility of policy management, without modifying Flash Access Java code.
Flash Access Implementation
Content Preparation
While preparing the content, please bear in mind that generally speaking, for online viewing and downloading you need different files. To download, you need a regular encrypted f4v file with access policy details added at encryption. For online viewing (Protected Streaming), an encrypted file with minimum access policy details is used, as the access is managed in the server configuration files. Moreover, after encryption you need to fragment the files to enable easy seeking of content without fully loading it.
Please note that Flash Media Server 4 enables fragmentation on the fly during encrypted content output. Also, it offers efficient mechanisms to manage content cache (if you try to implement them independently, you could face serious complications).
Standard License Server
The basic license server is used for offline viewing (download). The applicable policies are determined on data encryption and are embedded into a protected file. When a license is requested, the server uses the embedded policy of access restriction.
License Server for Protected Streaming
For online video viewing, Adobe offers a separate implementation, Flash Access for Protected Streaming. It applies the policies of content access restriction on the server side. In the near future, we will publish a separate detailed article on working with the server.
Load Balancing and Flash Access Fault-Tolerance
The license server uses the HTTP protocol, so it can easily be connected to a standard load balancer. In this scheme, it is also important to have a single point of decision making: the database or a central Web service (in this case, Flash Access Servers will be completely independent of each other). It is also easy to implement content preparation (encryption) in a distributed and fault-tolerant environment, provided there is a centralized content repository.
Typical Security Policies
Large copyright holders have quite similar requirements. Below we have outlined the most popular requirements and the principles of their implementation using Adobe Flash Access.
- Content availability timeframes — the basic parameters of content protection policies.
- Viewing window — the period of video availability from its first viewing.
- Level of protection for analog and digital outputs – these two parameters are fundamental to the access restriction policy and can take on four values.
- Application access lists — similar to Flash Media Server, this is client application verification. To implement it, you should provide Flash Access with fresh versions of client applications (swf and air) to verify them.
- License caching — Flash Access allows you to specify license caching settings so that users can watch video online without having to connect to a license server for some period.
- Authentication – whether the user is required to authenticate.
Wishing success to your online video business and many a loyal viewer.
